Let’s be real—the phrase “how to hack Instagram” gets typed into search bars thousands of times a day. But here’s the thing: most people asking aren’t malicious actors. They’re worried someone might hack their account, and they want to understand the threat. That’s smart thinking. Your Instagram account holds photos, messages, and connections you care about. If someone gains access, the damage can range from embarrassing to genuinely harmful.
This guide flips the script. Instead of explaining how hackers break in, we’re going to build a fortress around your account so strong that even if someone knows the tricks, they can’t get past your defenses. We’ll cover the real vulnerabilities Instagram faces, the tactics attackers use, and—most importantly—the concrete steps you take today to lock things down.
Why Your Instagram Account Is a Target
Instagram has nearly 2 billion monthly active users. That’s not just a social network—it’s a goldmine for attackers. Here’s why your account matters to them:
- Access to personal information: Your photos, location tags, and messages reveal habits, relationships, and routines.
- Impersonation opportunities: A hacked account can be used to scam your followers or spread misinformation under your name.
- Credential reuse: If you use the same password on Instagram and your email, one breach opens multiple doors.
- Selling stolen accounts: Hackers buy and sell compromised accounts on the dark web, especially business or influencer accounts.
- Accessing linked services: Instagram connects to Facebook, WhatsApp, and other Meta properties. One breach cascades.
You don’t need to be famous for this to matter. A regular person’s account is valuable because it’s trusted by people who know them. That trust is the real currency.
The Most Common Ways Hackers Gain Access
Understanding the attack vectors isn’t about learning how to hack Instagram—it’s about recognizing where the weak points are so you can reinforce them. Here are the real methods attackers use:
Phishing and Social Engineering
This is the #1 method. A hacker sends you a fake Instagram login page (looks identical to the real thing) via email, text, or a comment. You enter your credentials thinking it’s legit. Game over. The attacker now has your username and password. The FBI’s cyber division has documented phishing as the most common initial access vector for account compromises.
Password Reuse Across Platforms
You use the same password for Instagram, Gmail, LinkedIn, and that sketchy forum you joined in 2015. One of those services gets breached (this happens constantly). Attackers run your email and password combo against Instagram. Access granted. This is why password managers exist.
Weak or Guessable Passwords
“Instagram123” or “MyDogMax2024” might feel secure, but attackers use sophisticated dictionary attacks and pattern recognition. They test thousands of combinations per second. A weak password falls in minutes.
Unprotected Email Account
Your Instagram account is only as secure as the email attached to it. If someone hacks your email, they can reset your Instagram password instantly via the “Forgot Password” link. This is a critical vulnerability that most people ignore.
Third-Party Apps and Fake Login Tools
“Get free Instagram followers!” apps that ask for your login credentials? They’re stealing your password. Fake “Instagram growth” tools, story viewers, and analytics apps are common vectors. Never give your credentials to third-party services.
SIM Swapping and Phone Number Hijacking
If your Instagram is tied to a phone number, an attacker can call your carrier, impersonate you, and transfer your number to a new SIM card they control. They then use the “Forgot Password” flow and receive the verification code on their phone. It’s sophisticated, but it happens to high-value accounts.
Enable Two-Factor Authentication (The Non-Negotiable First Step)
If you do nothing else after reading this, do this one thing: turn on two-factor authentication (2FA). It’s the single most effective defense against account takeover.
Here’s how it works: After you enter your password, Instagram asks for a second form of verification—usually a code from an authenticator app or a text message. Even if someone has your password, they can’t get in without that second factor.
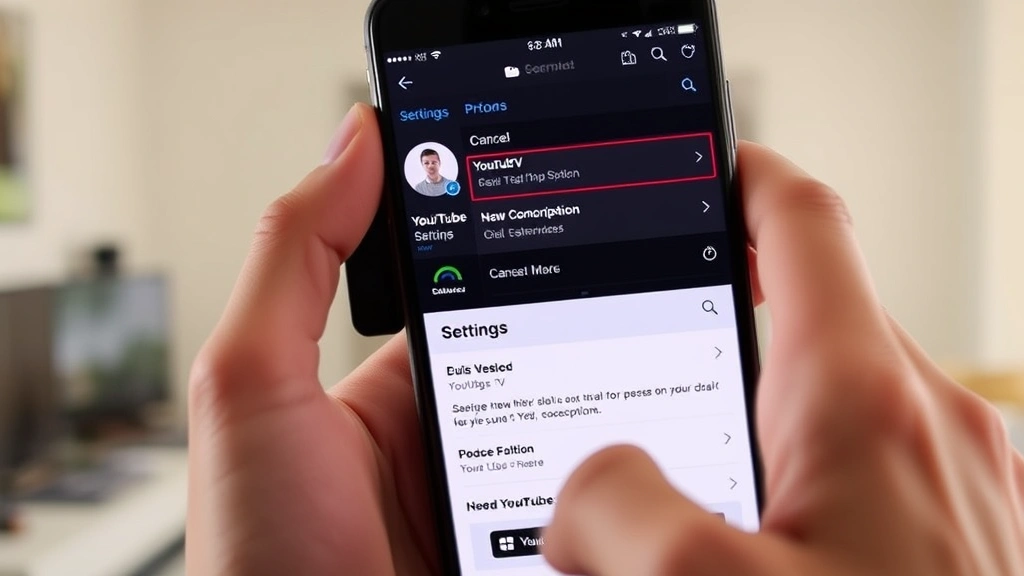
How to Enable 2FA on Instagram
- Open Instagram and go to your profile.
- Tap the menu icon (three horizontal lines).
- Select “Settings and privacy.”
- Go to “Security” and then “Two-factor authentication.”
- Choose your preferred method: authenticator app (recommended) or SMS (text message).
- If using an authenticator app, download one (Google Authenticator, Authy, or Microsoft Authenticator are solid choices) and scan the QR code Instagram provides.
- Save the backup codes in a safe place (not on your phone, not in an email).
Pro Tip: Use an authenticator app instead of SMS when possible. Text messages can be intercepted or redirected. An app-based code lives only on your phone and is far harder to compromise.
Instagram also offers a backup authentication method: security keys. If you’re serious about security, a physical security key (like a YubiKey) is the gold standard. It’s impossible to phish, and it’s what high-profile accounts should use.
Create an Ironclad Password Strategy
Your password is the first lock on the door. Make it count.
Password Rules That Actually Work
- Length matters more than complexity: A 16-character password with mixed case, numbers, and symbols is stronger than an 8-character one. Aim for 16+ characters.
- Avoid personal information: Don’t use your name, birthday, pet’s name, or anything someone could guess by looking at your Instagram.
- Don’t reuse passwords: Your Instagram password should be unique to Instagram. Period. If you use the same password everywhere, one breach compromises everything.
- Use a password manager: Services like Bitwarden, 1Password, or LastPass generate and store complex passwords. You only need to remember one master password.
Example of a Strong Password
Instead of “Password123,” try something like “BlueMountain$Sunset&Rain#2024.” It’s long, it’s random, it’s not in any dictionary, and it’s not connected to your personal life.
Safety Warning: Never share your password via email, text, or chat. Instagram support will never ask for your password. If someone claiming to be from Instagram asks for it, they’re a scammer.
Secure Your Email and Phone Number

Your email is the master key to your Instagram account. If someone gains access to your email, they can reset your Instagram password without your permission. Your phone number is the backup key. Both need to be locked down.
Protect Your Email Account
- Enable 2FA on your email: Gmail, Outlook, Yahoo—all support 2FA. Turn it on immediately. This is non-negotiable.
- Review recovery options: Go to your email security settings and verify the recovery email and phone number are ones you recognize and control. Remove any you don’t recognize.
- Check connected apps: In Gmail, for example, go to “Manage your Google Account” → “Security” → “Your devices” and review what’s connected. Remove anything suspicious.
- Use a strong, unique password: Same rules as Instagram apply here, but even more critical.
Protect Your Phone Number
- Contact your carrier: Ask them to add a PIN or password requirement for account changes. This prevents SIM swaps. It’s a free service most carriers offer.
- Don’t share your number publicly: Avoid posting your phone number on your Instagram bio or in comments.
- Be cautious with SMS-based verification: If possible, use authenticator apps instead of text-based codes for important accounts.
You might also consider turning off your active status on Instagram to reduce the information available to potential attackers about your habits and when you’re likely to notice account changes.
Review Connected Apps and Third-Party Access
Every time you use “Sign in with Instagram” on another app, or grant an app permission to access your account, you’re creating a potential vulnerability. It’s like giving a valet driver a key to your car—he should only drive it, but what if he makes a copy?
How to Audit Connected Apps
- Go to your Instagram profile.
- Tap the menu icon and select “Settings and privacy.”
- Go to “Apps and websites.”
- Review the list under “Active apps and websites.”
- For each app, ask yourself: “Do I still use this? Do I trust it?”
- Remove anything you don’t recognize or don’t use regularly.
Red Flags for Suspicious Apps
- Apps asking for permission to post on your behalf.
- Analytics or growth tools you don’t remember authorizing.
- Anything requesting access to your messages or email.
- Apps from unknown developers.
Pro Tip: Limit permissions. If an app only needs to read your profile, don’t grant it permission to post or modify content. Most apps request more access than they actually need.
Similarly, clearing your Facebook cache regularly can help remove tracking data and reduce the footprint these connected services have on your activity.
Monitor Your Account Activity and Login History
You don’t need to wait for a breach notification. Instagram provides tools to see who’s accessing your account and from where.
Check Your Login Activity
- Go to your profile → Settings and privacy → Security.
- Tap “Where you’re logged in.”
- You’ll see a list of devices and locations currently logged into your account.
- Recognize all of them? Good. If not, tap the three dots next to the suspicious entry and select “Log out.”
Review Login Alerts
Instagram can send you notifications when your account is accessed from a new device or location. Make sure this is enabled:
- Settings and privacy → Security → Login alerts.
- Toggle on notifications for new logins.
What to Do If You See Unfamiliar Activity
- Immediately change your password. Use a strong, unique password you’ve never used before.
- Log out all other sessions. Go to “Where you’re logged in” and log out every device except the one you’re currently using.
- Review your email and phone recovery options. Make sure no one has changed them.
- Check your connected apps again. Remove anything you don’t recognize.
- Enable 2FA if you haven’t already. This is your insurance policy.
What to Do If Your Account Gets Hacked
Despite your best efforts, it can happen. Here’s your action plan:
Immediate Steps (First Hour)
- Try to log in: If you can still access your account, change your password immediately and enable 2FA if it’s not already on.
- Use the “Forgot Password” flow: If you can’t log in, go to the Instagram login page, tap “Forgot password,” and follow the recovery process. You’ll need access to your email or phone number.
- Contact Instagram support: Go to the Help Center within the app or use the web form at help.instagram.com. Report that your account has been compromised. Provide as much detail as possible.
Notify Your Contacts
If your account was used to send phishing messages or scams to your followers, let them know. Post a story or send direct messages to close friends warning them that your account was compromised and they should ignore any suspicious messages from you.
Check for Damage
- Review your recent posts. Did the hacker post anything? Delete it.
- Check your Direct Messages. Did they message anyone? Apologize and explain.
- Review your bio and profile picture. Were they changed?
- Check if your email or phone number were changed. If so, change them back immediately.
Prevent It From Happening Again
- Change your password to something completely new.
- Enable 2FA with an authenticator app.
- Review all connected apps and remove anything suspicious.
- Check your email account security. If your email was compromised, that’s the root issue.
- Consider changing the password on any other accounts that share the same password.
Safety Warning: If you’ve lost access to your email and can’t recover your Instagram account, you may need to provide Instagram with identity verification (a photo of your ID). This is a slower process, but it’s Instagram’s way of preventing attackers from permanently locking you out.
If your account was used for fraudulent activity, the Federal Trade Commission recommends reporting identity theft to their website if personal information was compromised.
Frequently Asked Questions
Is it possible to hack an Instagram account with two-factor authentication enabled?
– Technically, yes, but it’s exponentially harder. An attacker would need to compromise your authenticator app, intercept your phone number, or use sophisticated social engineering against Instagram support. For practical purposes, 2FA makes your account a much less attractive target. Hackers move on to easier prey.
What should I do if I receive a suspicious email claiming to be from Instagram?
– Don’t click any links. Go directly to Instagram.com or open the app on your phone instead. Legitimate Instagram communications will never ask for your password or direct you to a suspicious link. If you’re unsure, contact Instagram support directly through the app.
Can Instagram be hacked if I use a VPN?
– A VPN doesn’t protect your Instagram account specifically. It encrypts your internet traffic, which is good for privacy, but it doesn’t prevent phishing, weak passwords, or compromised recovery emails. A VPN is one layer of security, not a complete solution.
How often should I change my Instagram password?
– You don’t need to change it regularly if it’s strong and unique. Change it if you suspect a breach, if you’ve shared it with someone, or if you’ve used it elsewhere. The old advice to change passwords every 90 days is outdated. A strong password that never gets reused is better than a weak password changed frequently.
What’s the difference between being hacked and having your account cloned?
– Being hacked means someone gains access to your actual account and can post, message, and change settings. Account cloning is when someone creates a fake account impersonating you but doesn’t have access to your real account. Both are problems, but hacking is more serious. You can report fake accounts to Instagram and ask your followers to report them as impersonation.
If I see “how to hack Instagram” in search results, does that mean it’s easy?
– Not necessarily. Search results include articles about security, educational content, and yes, some guides written by people with questionable intentions. The fact that information exists doesn’t mean it’s reliable or that the methods work. This is why understanding real security practices matters more than worrying about every possible attack vector.

Should I delete my Instagram account if I’m worried about hacking?
– Deleting your account is the nuclear option and usually unnecessary. If you follow the steps in this guide—especially enabling 2FA, using a strong password, and securing your email—your account will be dramatically more secure. You can take a break from Instagram without deleting it. If you do decide to delete, Instagram offers a 30-day deactivation period where you can change your mind.
Can I recover my Instagram account if the hacker changed my email and phone number?
– Yes, but it takes longer. You’ll need to contact Instagram support and provide identity verification (a photo of your ID). This process can take days or weeks, so prevention is really the better strategy. That’s why securing your email and phone number is so critical.